Websites have been around for decades now. But earlier, website owners (or hosting providers) were only concerned about securing their infrastructure from hackers, viruses, and malware. Why? To protect the servers and the websites hosted on them. Very few businesses – primarily banks and payment processing companies – would go a step further. They would ensure their customers’ safety by securing the communication between them and their websites.
One day, however, something changed! Suddenly, every website owner started implementing HTTPS with SSL certificates on their websites. Let’s understand more about Internet Safety and how HTTPS works.
1. How do our browsers communicate with websites?
Most of the communication on the Internet happens using a protocol called HTTP (Hypertext Transfer Protocol). Your web browser (e.g., Chrome, Firefox, etc.) also talks to all the websites you browse over the same protocol. This is termed a Request-Response protocol. Here, your browser ‘requests’ for information from the website. The website ‘responds’ with the required information.
The browser then displays this information on your screen. This protocol uses different methods (like GET and POST, etc.) to send and receive data between your browser and the server. HTTP is the most commonly used protocol. This is due to its ease of implementation in making two disjoint systems talk to each other. However, HTTP in its basic form is highly vulnerable when used over a public network (Internet).
2. Drawbacks of HTTP Protocol
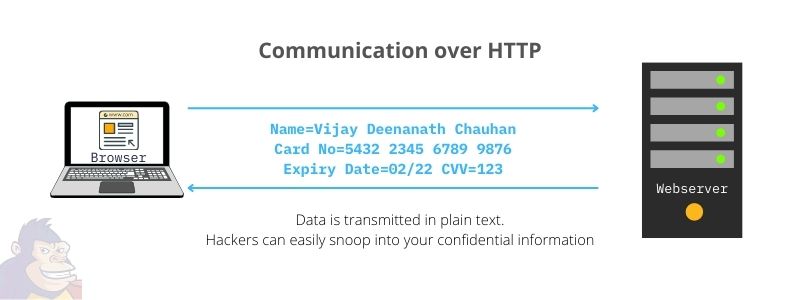
HTTP is natively a Plain Text protocol. That means all the information exchanged between your browser and a website is in plain text. So, let’s say hackers have gained access to any networking systems through which your communication is happening (wifi routers, proxy servers, etc.). They can now potentially read and misuse the information.
Imagine that you are on an e-commerce website. You are entering your credit card information to make a purchase. Your credit card number, CVV / PIN, etc., are being transmitted in plain text to the server. Not comforting at all, right? That’s where HTTPS comes to the rescue.
3. How is HTTPS different?
HTTPS stands for HTTP over SSL (Secure Sockets Layer). Here, the idea is to use the robust and easy HTTP protocol without compromising on security. In HTTPS, the browser and the website still use HTTP as the underlying protocol to communicate. Here, however, the information exchanged is encrypted. Only the two communicating entities (browser & the website) can understand what the other is saying.
What happens if any other entity or a hacker manages to eavesdrop on the communication? All that (s)he will see is garbled, meaningless text. This provides reasonably good security to the users of banks, e-commerce, and other such websites.
4. How do you know if a website you are visiting is safe?
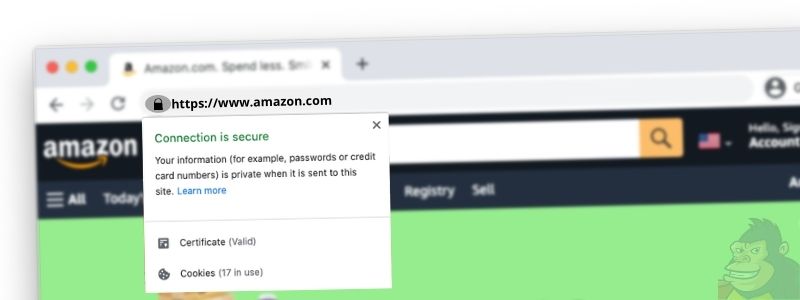
Let’s keep this simple. When you visit a website, check if its address in the browser shows “https://<website name>â€. Also, check if a closed padlock icon appears next to it. Then, you know the communication is encrypted. If the website has a valid SSL certificate and the website’s organization has been verified by a Certificate Authority, the padlock will be green in color. This might look slightly different on different browsers, though.
5. What is an SSL Certificate?
It is vital to ensure that the information you exchange with a website is encrypted when browsing the Internet. But it is even more critical to ascertain that you are talking to the correct website and not a fake or a look-alike website! In that case, you might be handing over your security details directly to fraudsters – albeit over an encrypted channel.
To solve this issue, web servers supporting HTTPS use an SSL Certificate to prove their identity to the visitors (browsers). An SSL certificate primarily contains information about the Organization, the server and verified domain name, etc., along with a digital signature or cryptographic key.
The certificate also includes endorsements (or certificate chains) issued by trusted global certificate authorities (CA). These further assure the authenticity of the SSL certificate. Browsers use this certificate to verify that the website they are talking to is genuine.
6. Heads up on encryption techniques
The most common encryption techniques used to communicate on public networks are Asymmetric Key and Symmetric Key Cryptography.
6A. Asymmetric Key
In Asymmetric Key encryption (also known as Public Key Cryptography), each entity or user has a pair of keys – Public Key and Private Key. When two users (sender and recipient) communicate with each other, they first exchange their respective Public keys in a process called public-key-exchange or a key-handshake.
The sender then uses the recipient’s Public key to encrypt his messages before sending them to the recipient. These messages can only be decrypted by the recipient’s private key (which is never exposed or transmitted on the public network). Hence no other entity in between can decipher the messages exchanged between the two parties.
6B. Symmetric Key
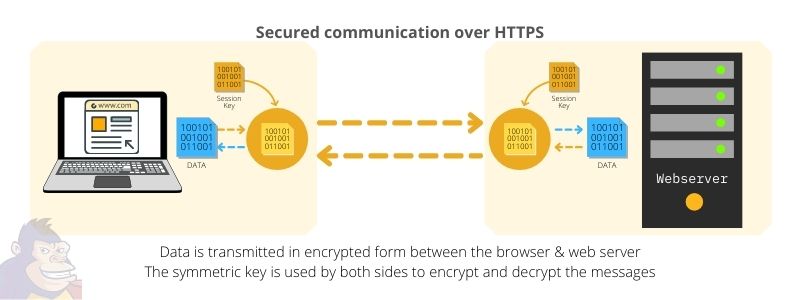
On the other hand, Symmetric Key encryption uses only one key to encrypt and decrypt the messages. In this case, the sender and the recipient share the same key to encrypt and decrypt messages exchanged between them. This method is easier to implement and much quicker than asymmetric encryption.
However, this works only when the common secret key is already with both the entities before the communication is initiated. In HTTP-based communication, the web server and the various browsers cannot possibly possess every other entity’s symmetric key beforehand. (That would be a nightmare to securely manage keys of millions of websites and billions of browsers).
Hence, HTTPS communication uses a combination of both these methods. Firstly, the browser and the web server use the Public key method to initiate a secure connection between them. This is just to send its Symmetric key to the web server over a secure channel (encrypted by the server’s public key).
Once the web server receives the symmetric key, they start talking to each other using the same key on both ends for encryption and description. This is much more efficient and secure enough for communicating over public networks.
7. How exactly does HTTPS work then?
Now you know what HTTPS is and what an SSL certificate contains. We have also seen what encryption techniques are used to communicate over HTTPS. So, how does it work when you browse the internet, access your bank’s website? Or even when you make payment transactions on “secure†websites like Amazon, eBay, Flipkart, etc.?
Here’s how it happens.
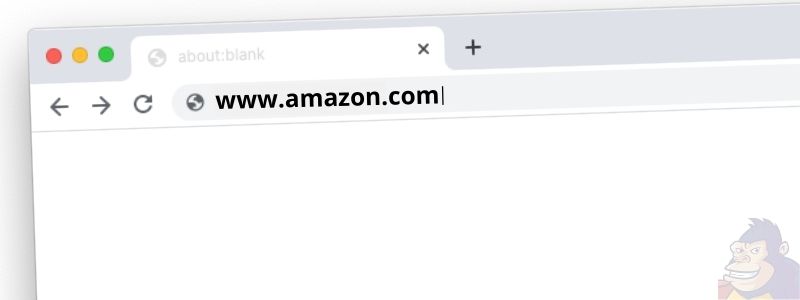
Step 1: First, you try to visit a website by entering its address in your browser – let’s say ‘www.amazon.com’ Your browser connects to Amazon’s web server and requests its identity information.

Step 2: Amazon’s web server identifies itself to your browser by sending its SSL certificate. This contains its Organization name and domain verification data (certified by a trusted Certificate Authority). It also includes its Public Key (explained in the section above) that will be used by the browser later. This communication is still unencrypted – but it’s okay as there is no sensitive information exchanged yet.
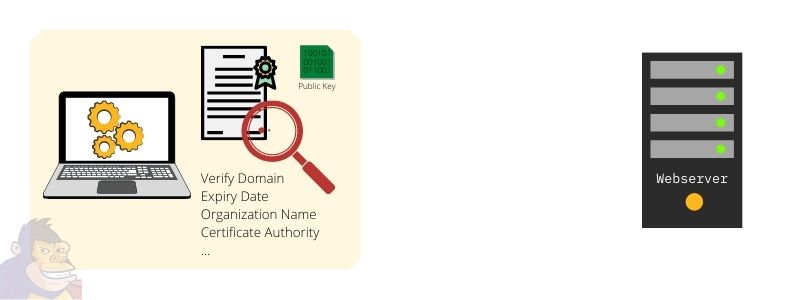
Step 3: The browser reads the SSL certificate sent by the server and verifies that it is valid – domain match, expiry date, etc. It also confirms that the certificate is authenticated by a trusted authority (CA). It does so by comparing the CA’s digital signature in the certificate chain with the ones available in its database. (All browsers have a preloaded set of keys belonging to top-level CAs).
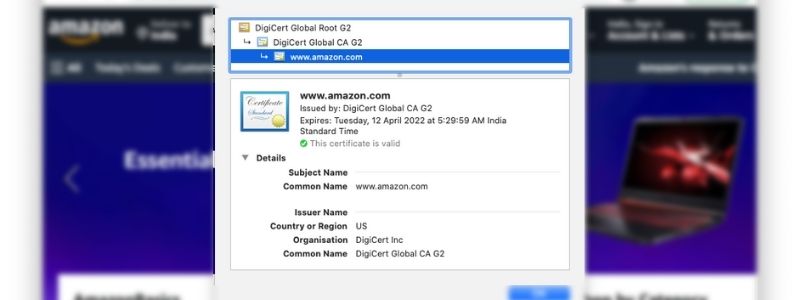
Once the certificate is validated, the browser shows ‘https://’ in the address bar. There will also be a green padlock icon next to it – indicating that the web server’s identity has been verified.
Note that at times the padlock might be grey and not green. This depends on the level of certification obtained by the website owner. Not all websites need Extended Verification of the organization that owns the website. Hence, a grey padlock is perfectly fine for blogs or regular business websites. However, in the case of Internet banking, payment gateways, e-commerce, etc., a green padlock would mean a safer experience for you.
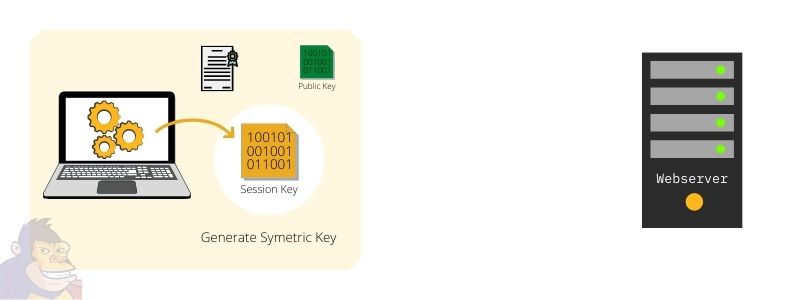
Step 4: The browser now generates a secret key (the symmetric key) for encryption and decryption. It has to securely send a copy of this key to the web server. That’s when the public key received along with the SSL certificate comes in handy.
The browser encapsulates the symmetric key in a message encrypted using the server’s public key and sends it to the web server. This is safe because only the web server (in our example, Amazon) has the private key to decrypt the message. Thus, the symmetric key has been safely shared with it.
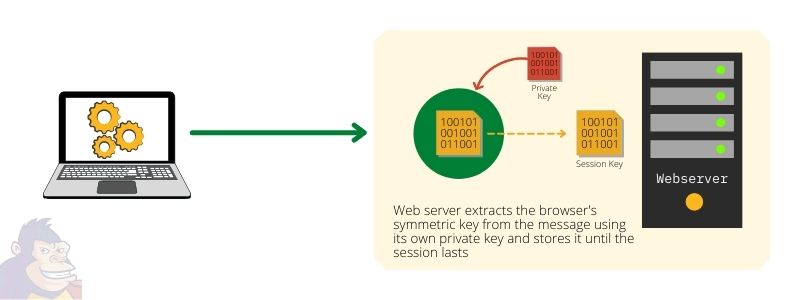
Step 5: The web server receives the encrypted message containing the browser’s secret key and creates a new session for this connection. All further communication with this browser will now be encrypted and decrypted using this key only.
The same happens on the browser as it encrypts and decrypts all messages sent and received from this server using the same key. Both the browser and the web server will retain the key only as long as the session is active.
8. What about the hint in the intro? What made everyone switch to HTTPS?
Yes, we’ll get to that now. Technically, not everyone needs encryption and SSL security. Static websites, blogs, portfolio websites, etc., and those who do not exchange sensitive information with the users don’t need an SSL certificate or communicate over HTTPS. However, not one but three significant reasons convinced everyone to switch to HTTPS.
- More and more fraudulent websites started imitating genuine ones. They started fooling users and stealing their sensitive information (like credit cards, bank passwords) or created fraudulent transactions. So, it became necessary for genuine websites to authenticate themselves by using SSL certificates. Why? To build the trust of their customers!
- For the same reason mentioned above, almost all modern browsers (starting with Google Chrome) started to warn their users. Their pop-ups alerted users when they visited websites without SSL, saying that their communication was ‘Not Secure.’
- However, the most prominent reason was that Google started penalizing websites that did not use SSL by not showing them in its search results. This was the game-changer.
8A. Internet Security Research Group
Another key reason was that until recently, SSL certificates that were authorized by a handful of commercial CAs were costly. Most bloggers and small business owners could not afford the high recurring fees to maintain these SSL certificates.
This changed when a non-profit organization, Internet Security Research Group (ISRG), started an automated open Certificate Authority service. Called “Let’s Encrypt,†it provided free SSL / TLS certificates to website owners. The only limitation is that they do not offer ‘Organization Name’ and ‘Address’ verification. Also, their certificates need to be renewed every 90 days.
9. Is this how end-to-end encryption of WhatsApp also works?
Well, not exactly. WhatsApp and other similar apps use the Asymmetric Key Cryptography method. Here, the two end-users (apps on the phone) generate and use a pair of keys (Public and Private keys) and exchange their public keys with each other. This enables them to encrypt and decrypt the messages between them. This is done such that no other entity (even WhatsApp servers) can decrypt them.
Read more about how this works in our article on End-to-End Encryption: What you need to know in 7 easy steps .
If you are looking for a secure, robust, and affordable web hosting service with a free SSL certificate and fantastic support, then check out HOSTINGER.COM
Are you looking at creating or upgrading your website with the latest designs, mobile-friendly layouts, and modern functionality? Get all of this at pocket-friendly prices! Check out the Website Design Packages from our digital marketing partners MediaGhar for a hassle-free experience. Use coupon code APE10 to avail discount of 10% on various products.